F5 BIG-IP SSL Orchestrator Training Lab > Class 1: SSL Orchestration > Module 3: Service Policies Source | Edit on
Lab 3.1: Reviewing the Policies¶
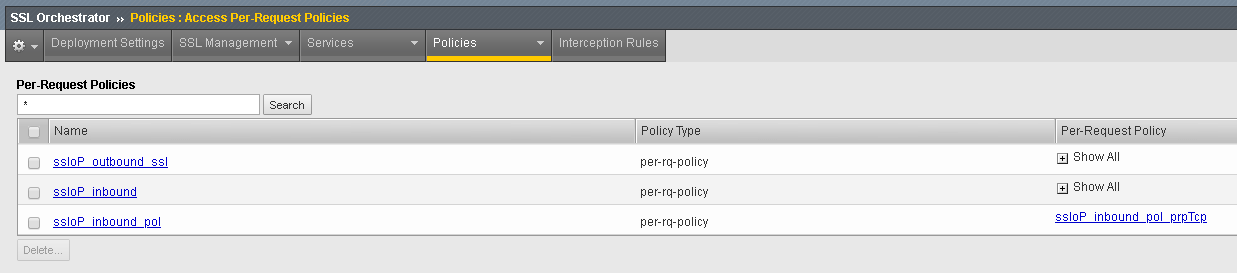
Task 1 - View the Per-Request Policies¶
Login to the BIG-IP with Firefox
Navigate to
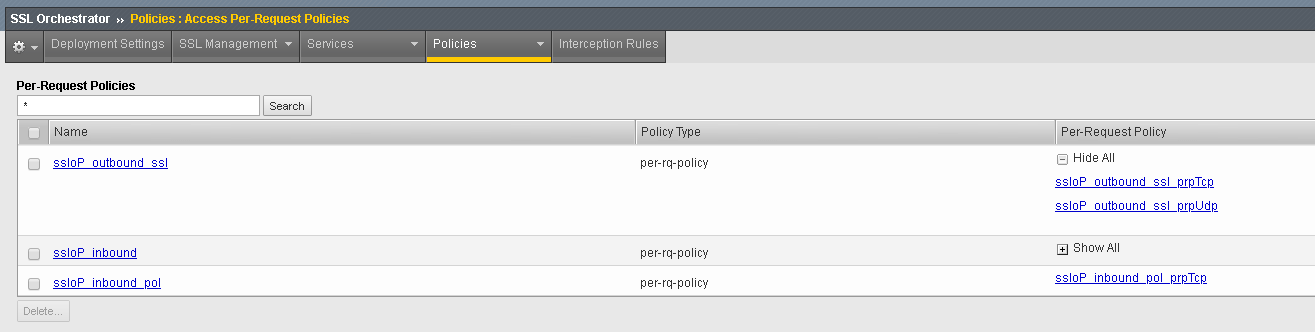
Click the plus sign next to Show all for the ssloP_outbound_ssl row
Select the ssloP_outbound_ssl_prpTcp Per-Request policy
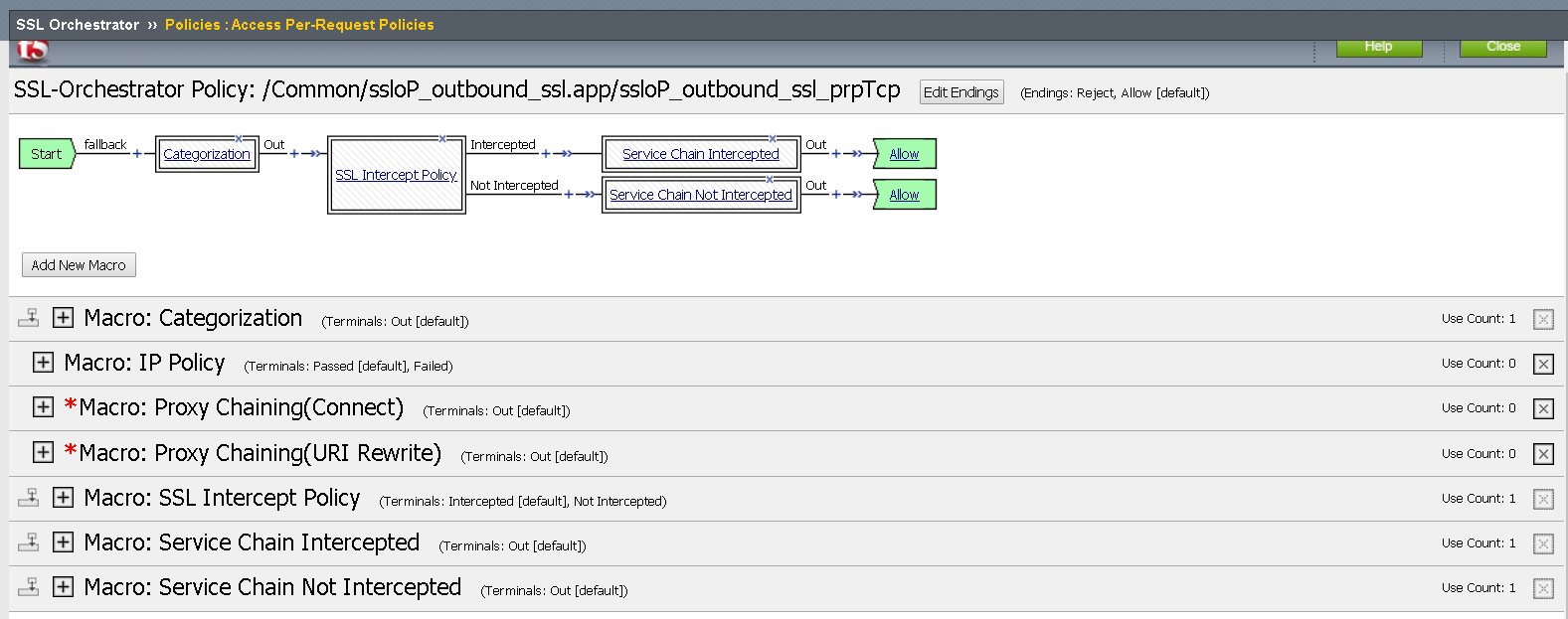
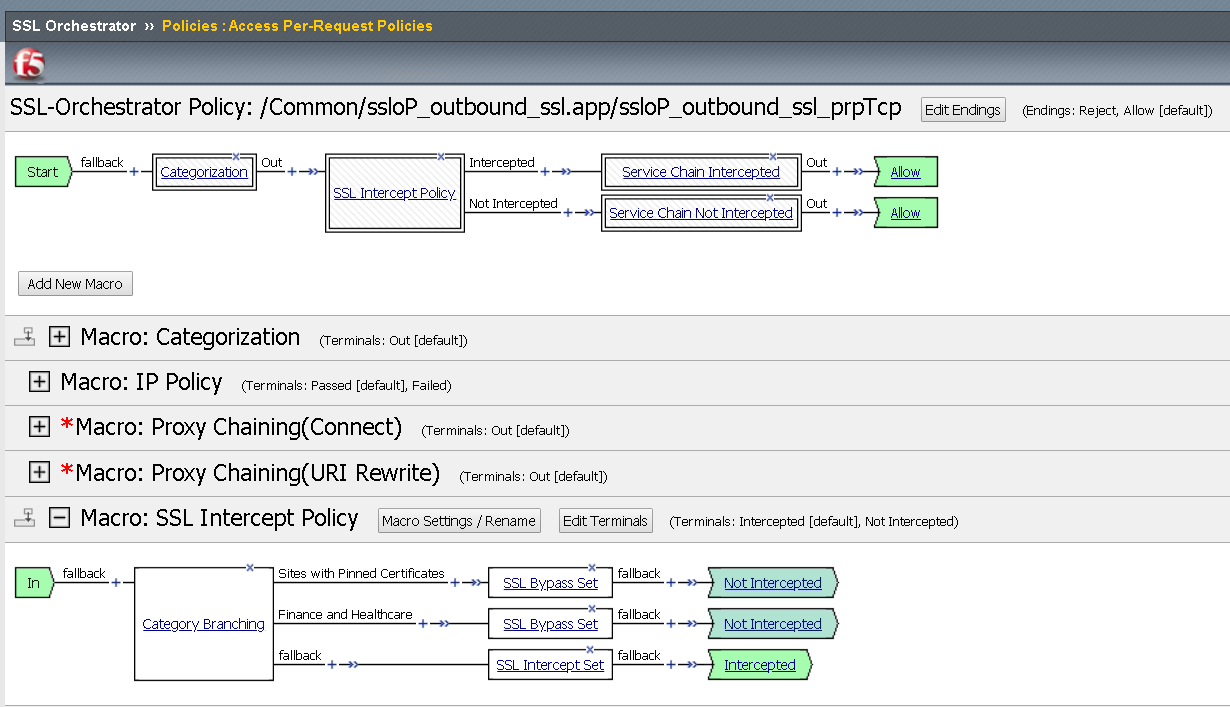
Review the general flow from categorization through Intercept policy to Service Chain
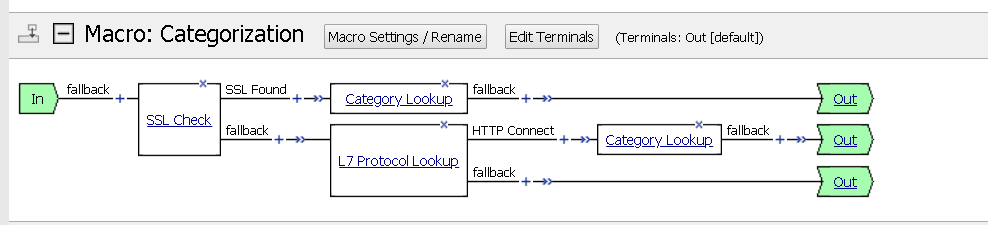
Expand the Macro: Categorization macro by clicking on Categorization in the boxed area or the plus symbol in the macro section.
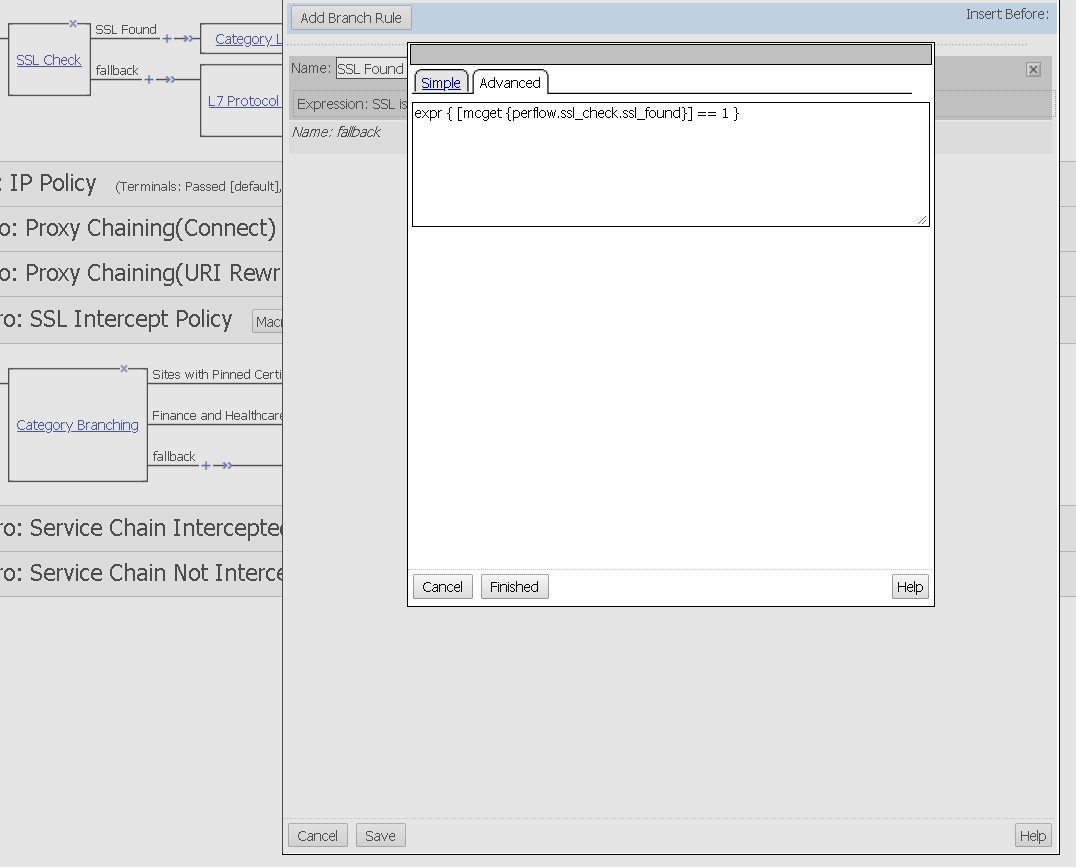
Explore the SSL Check advanced Action Properties
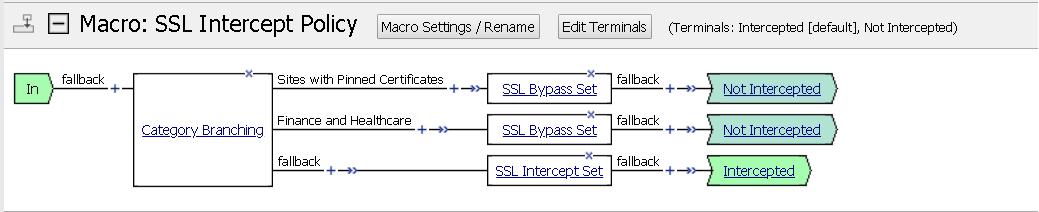
Expand the SSL Intercept Policy macro. Notice that the Not Intercepted and Intercepted terminal endings differ based on the category and setting interception.
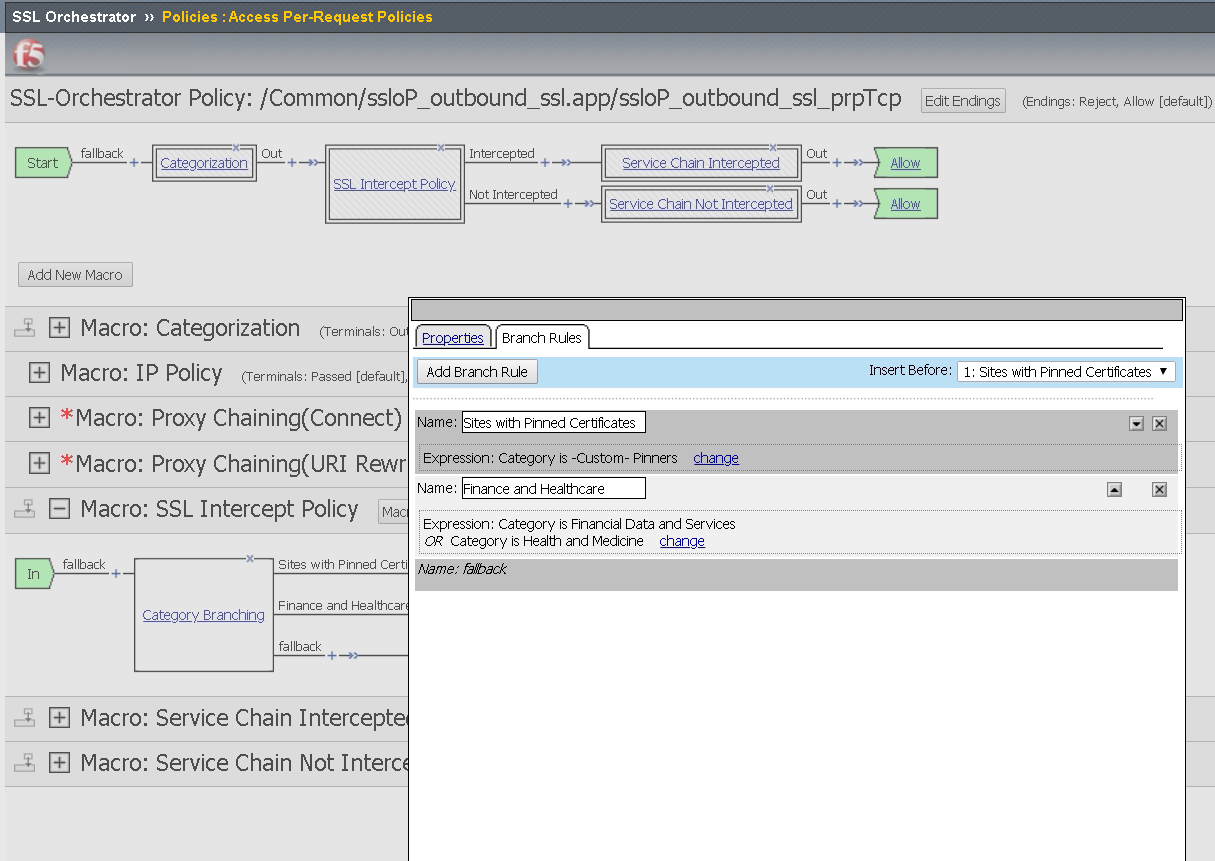
Explore the Category Branching Action Property
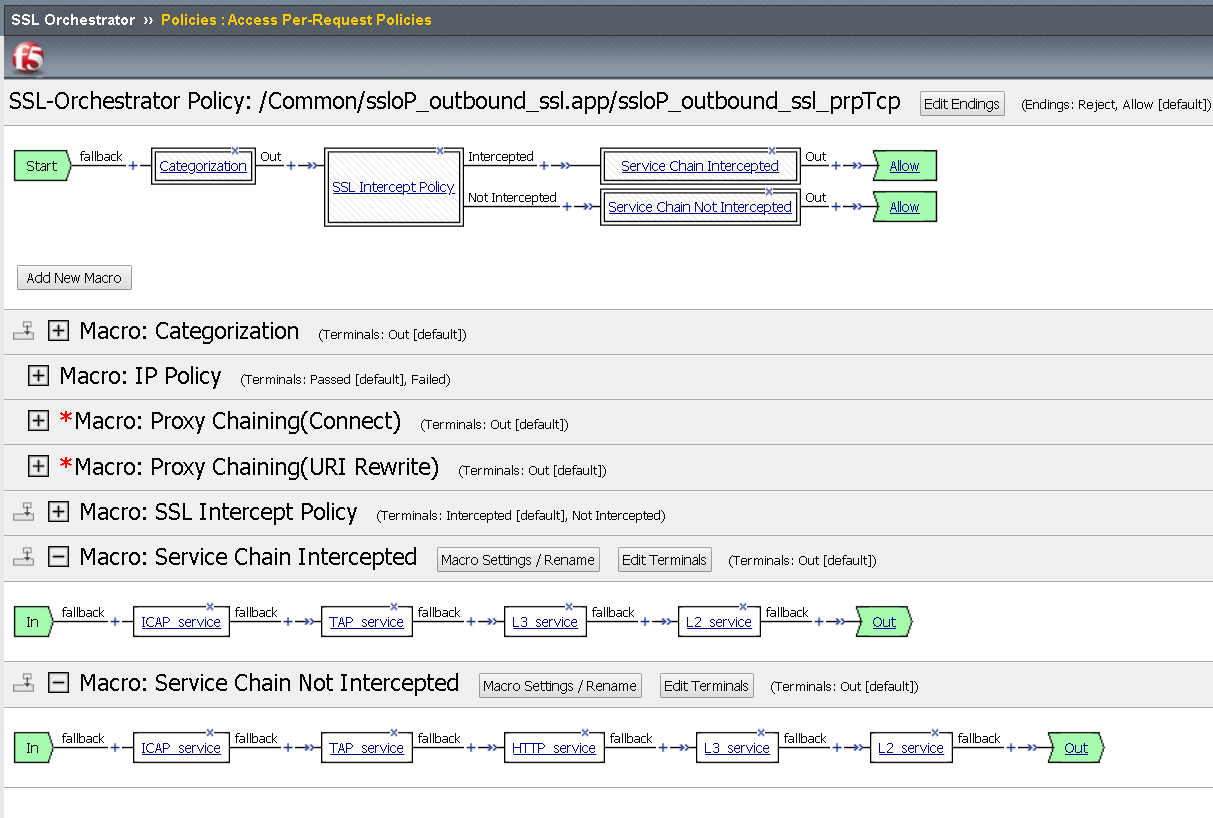
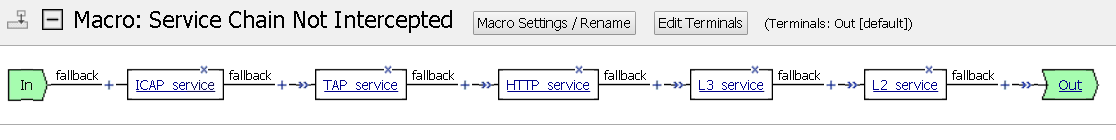
Expand the macros Service Chain Intercepted and Service Chain Not Intercepted
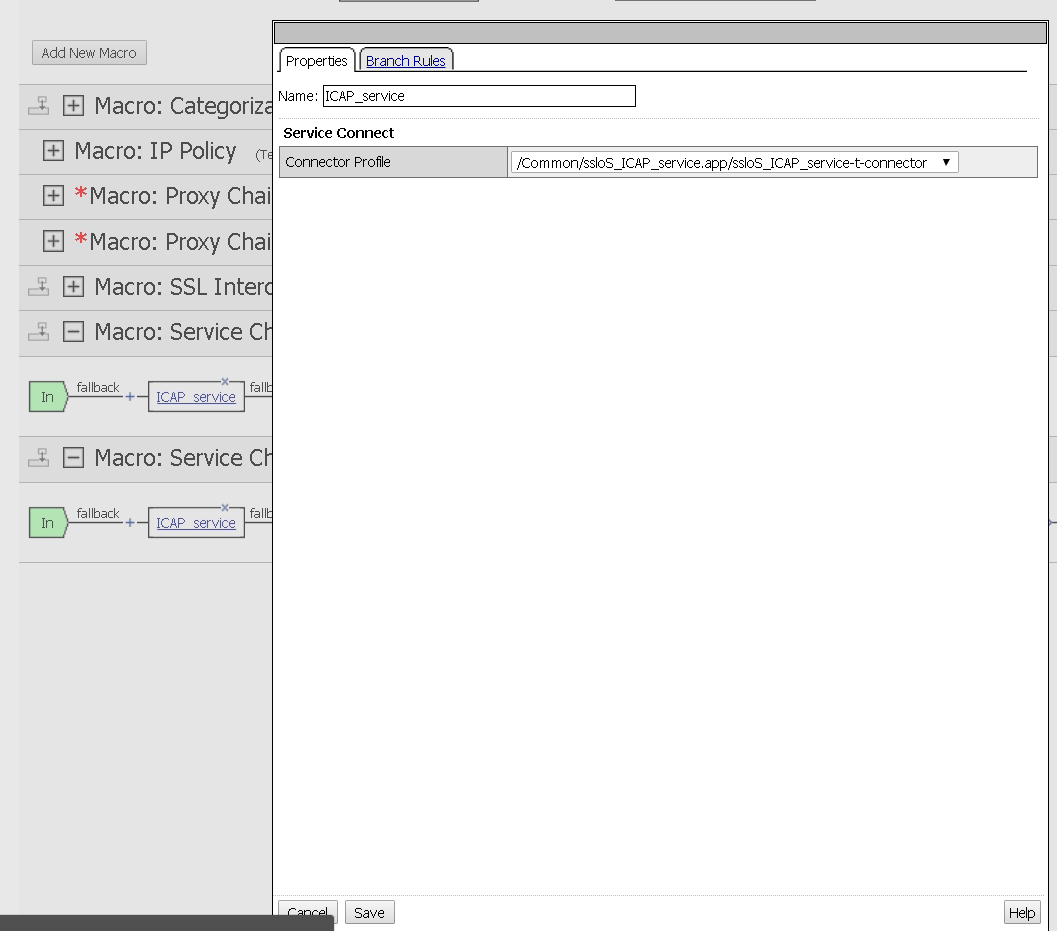
Explore the Action Properties in the Service Chains and notice the Connector Profiles
Task 2 - Modify the Intercept Policy¶
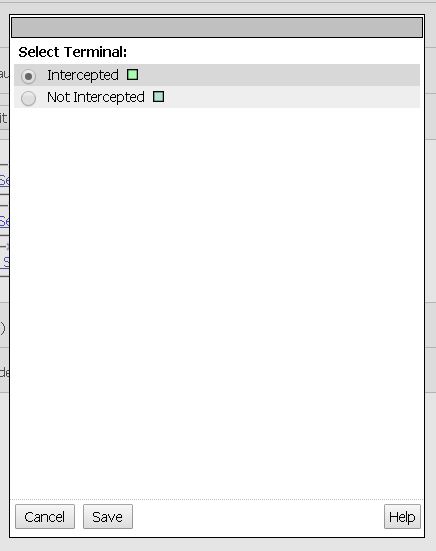
Expand the macro SSL Intercept Policy and click the Intercepted terminal ending
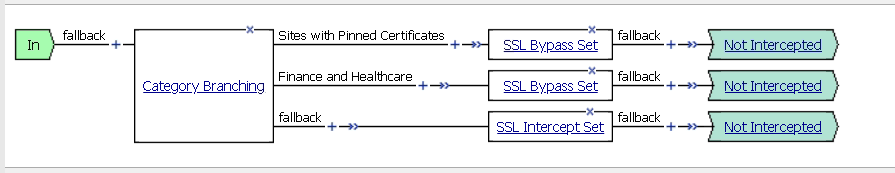
Select the Not Intercepted radio button, then Save
Repeat the test from Lab 1.8 and notice that traffic is not decrypted. Notice that this had the impact of all traffic bypassing inspection zone.
Undo the change by setting the terminal ending back to Intercepted and repeat test.
Task 3 - Modify Service Chain¶
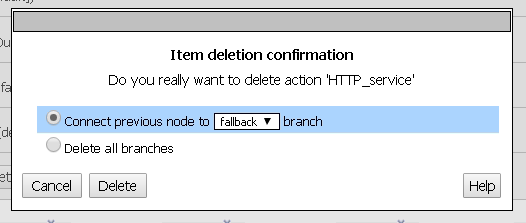
Expand the macro named Service Chain Not Intercepted and remove the HTTP Service node by selecting the X in the corner. The X will turn red when you hover over it.
Click the Delete button in the Item delete confirmation dialogue box
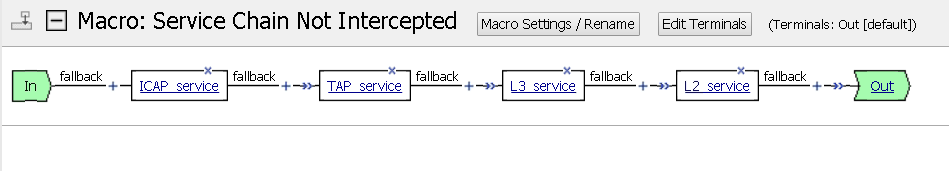
View your results
Add the HTTP Service node back by selecting the plus key between TAP and L3 services
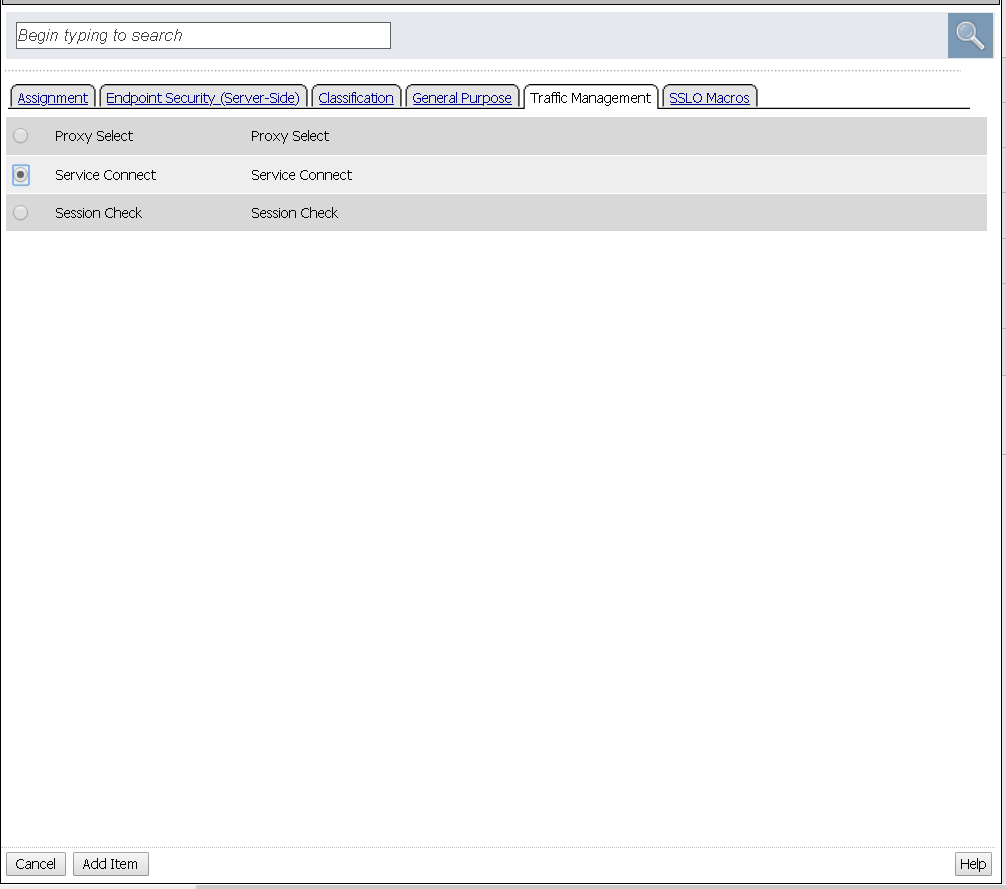
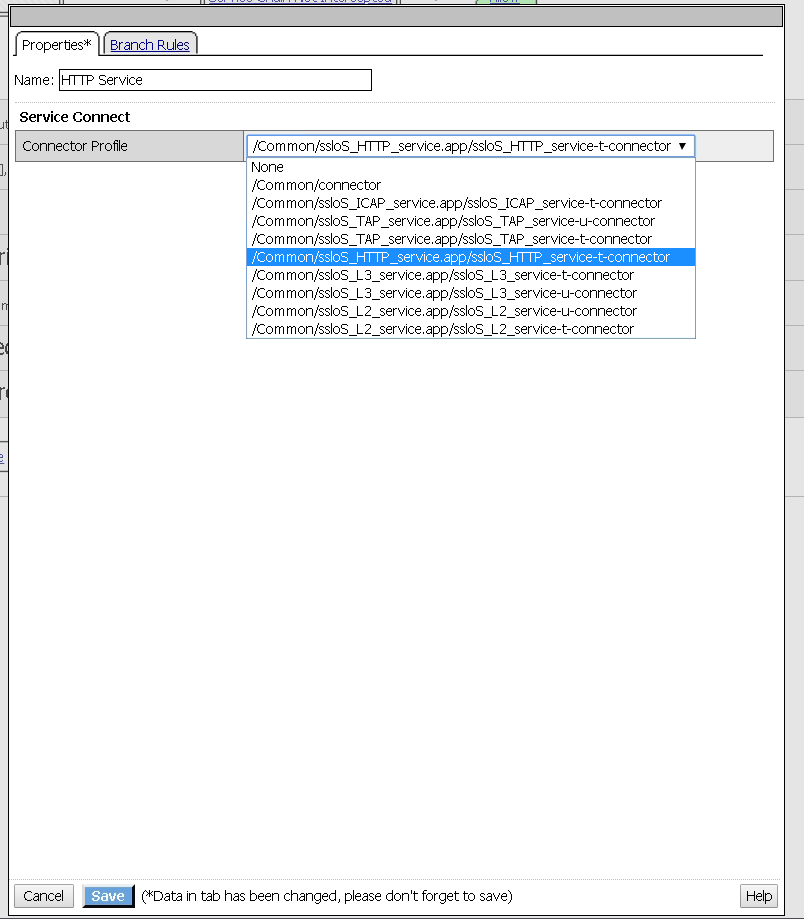
Select the Traffic Management tab, then the Service Connect item and click Add Item
Change the Name to HTTP Service, choose the HTTP Service item from the Connector Profile drop down menu named /Common/ssloS_HTTP_server.app/ssloS_HTTP_service-t-connector and then click Save at the bottom